Previously, I told you about the DNS DDoS cannon that was responsible for taking out the internet in the U.S. and parts of Europe. The hackers whom I suspected were the ones responsible — the New World Hackers — have come forward. We had a very informative final interview, one that showcases the weaknesses in our network security, and a very large flaw in the structure of the internet itself.

I once had an intriguing conversation with a claimed Lulzsec hacker. He told me simply, “Security doesn’t exist. It’s an illusion. Every system is exploitable. It’s just a matter of time.”
Although it was just a DDoS attack, and it wasn’t a hack, the devices that were used were directed packets at DYN DNS servers and targeted website servers, last Friday. The attack was historic — never has such an attack occurred. It was practically genius, hitting DYN DNS servers responsible for translating over 150,000 websites from their numerical IP addresses to domain names. The attack also claimed popular sites as targets. It was truly impressive. Despite only lasting for a short duration, it topped the record books.
New World Hackers tweeted out an image of how much bandwidth they were hitting Twitter.com with shortly before it went down — 1,256.54 GB/s alone. An unheard-of amount of bandwidth.
Twitter is suffering.. pic.twitter.com/wE2KFQkUPs
— New World Hackers (@NewWorldHacking) October 21, 2016
New World Hackers tested their DNS cannon earlier this summer when they took out the BBC. That test attack hit a mere <i< a=””>>602 Gbps on the BBC’s website, compared to the recent attack which hit — according to the hackers — 1.5 Terabytes a second, an insane amount of bandwidth. Aimed at each target, it would instantly make any website in its cross-hairs sh*t itself from being overwhelmed with traffic requests.
The group also announced its retirement from hacking, telling me that they didn’t want any of their members to go to jail for the attack, like the infamous PoodleCorp, and they are calling it quits.
“
The stakes are too high to just continue attacking people and end up getting arrested like Poodle Corp. This was a reality check for us, no need to spend any time in jail.”
Before they called it quits, though, they offered me a final exclusive interview. That full interview is below.
New World Hackers also discussed what devices were compromised for the attack. And it might scare you with a reality check.
Additionally, they provided me with the motive for the attack. Strangely enough, it’s the most confusing reasoning I’ve ever heard.
They claimed their attack was to showcase their power to the Russian government, insinuating that if they were crazy enough to do what they did, once, they would most likely do it again, if needed, to the Russians. If, in their own words, “They [the Russians] continue meddling in U.S. elections.” New World Hackers also said that Wikileaks was their “friend” and that they would “leave that statement as is.”
Wikileaks also apologized for the outage, blaming its supporters. And, well, Wikileaks was right….
Goodbye, old friends. Rest in power. Sail safe, and bon voyage, in the proxy seas.
We want everyone to read this, goodbye. pic.twitter.com/YCiewVC1Kt
— New World Hackers (@NewWorldHacking) October 23, 2016
Question and Answer:
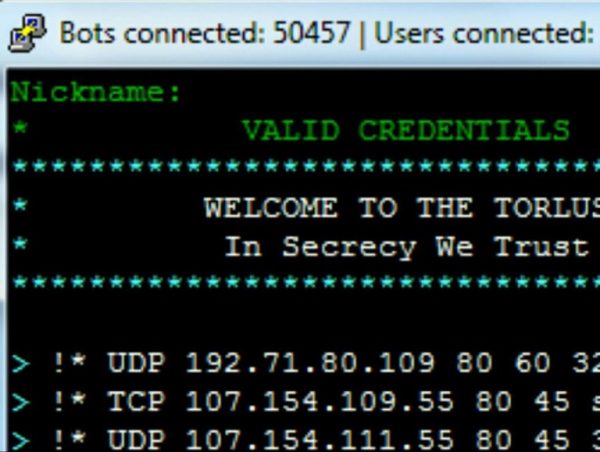
How did you accomplish the attack? Botnets? Or was it Mirai?
And why attack the internet’s infrastructure? Did you realize that attacking the DNS servers at DYN would drop so many sites at once? That’s one of the most impressive hacks I’ve seen in a long time.
“We used our own special coded supercomputer botnets and also Mirai to pull off such an attack. We have known for years that if you are able to pull off an assault on a DNS server it would drop the website or series of websites that domain name server holds. If you use a DNS amp on a botnet, it is extremely powerful.”
So you pull off the biggest Cyber Attack in History, topping 1.5 Terabytes a second, and hang it up?
What was the reason for the attack? Does it have to do with Twitter’s recent censorship and, in general, the censorship of social media? Or how about the recent handing over of ICANN to the U.N.?
“The stakes are too high to just continue attacking people and end up getting arrested like Poodle Corp. This was a reality check for us, no need to spend time in jail. The reason for this attack was simply because Russia is against the U.S. We wanted to send Russia a warning, so they would think twice before performing cyber attacks against the U.S. Wikileaks is our friend, also, and we will leave that statement as is.”
So this was a warning shot at Russia while attacking the U.S. That’s ironic. Don’t you think?
“Somewhat. We do think it’s ironic. But this shows them we are crazy enough to attack them also.”
What devices were used during the attack? Did you infect cameras, DVR players, and smartphones, as many mainstream media outlets are claiming?
“Cameras, laptops, computers. Anything that was accessible or vulnerable to the botnet exploit was added onto the IoT botnet.”
That’s amazing. How long did it take for systems to get infected to the point where you knew it was strong enough to take out the U.S. east coast internet during the morning, and parts of the west coast and Europe during the afternoon?
How does it feel to know that you guys broke a world record, and that you can now be added to the Guinness Book Of World Records? That was single-handedly the world’s largest cyber attack. Do you believe that by achieving the attack you exposed a key flaw in the internet’s infrastructure, and essentially helped to fix a potential problem before it got worse or was used by state actors during cyber war?
“It took us months, and that’s why the people who actually tuned into us before this big attack didn’t see big attacks earlier. We worked on this all summer and made sure it ran smoothly. We performed multiple tests…
It feels extreme, being able to look back on something like this. You never would have thought that this could happen. But with hard work and dedication it happened. We honestly think we did show the world the vulnerability in systems today and that kind of brought a smile upon our faces.”
If I remember correctly you guys took down the Guardian earlier this year, right?
What are some of the other sites you took down in those previous tests, before the big one?
“The internet relies on DNS servers to function, but that isn’t helping. Something else needs to be put in place of DNS servers. We didn’t take down the Guardian. But at one point, we took down BBC and ZDNET for short periods of time.”
Did you guys only attack DYN or did you hit the DNS DYN servers and individual websites at the same time?
“We hit DYN, which held off Playstation, Paypal, and the others. Twitter was lagging from DYN and we noticed Netflix was too. We went ahead and just attacked those two as well to see what would happen. We then got nervous and attacked http://map.norsecorp.com so some people couldn’t monitor the DDOS attack.”
/end interview.









Sign up on lukeunfiltered.com or to check out our store on thebestpoliticalshirts.com.